V4cnyy Ransomware Drops a Russian Language Ransom Note
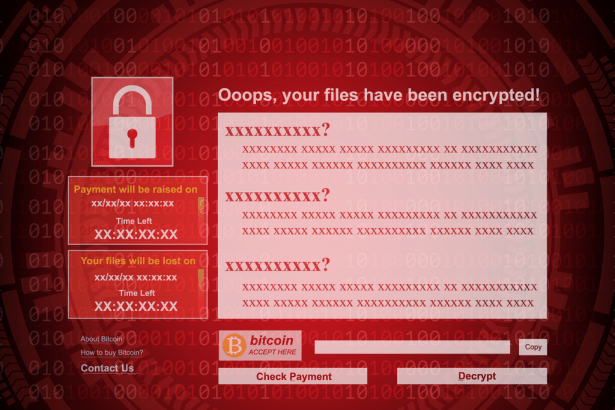
Being infected with ransomware is bad enough, but imagine having your critical files encrypted and then not even being told the hackers’ demands. This may eventually happen to you should you be victimized by V4cnyy Ransomware. V4cnyy Ransomware is a threat that works in the way most ransomware strains operate.
It locks its victims’ files and then attempts to extort them for a ransom payment. V4cnyy Ransomware can affect many file types and uses a strong encryption algorithm. Although the V4cnyy Ransomware we are talking about here is thought to be in the testing stage of its development, this version is nevertheless deployed by hackers, and incidents related to it are growing in frequency. Although it seems to be targeting Russian-speaking victims, computer users globally should still be wary of this nasty infection.
During the encryption process, V4cnyy Ransomware reveals itself by changing the names of affected files by appending ‘.v4cnyy’ to them as a new extension. V4cnyy Ransomware then creates a text file named ‘-Инструкция.txt’ on the victim’s computer. Translated from Russian, the name means “instruction” and contains a ransom note. Perhaps because this version of the ransomware is still in development, the ransom note file is actually empty.
Victims are still presented with a message displayed before the system’s log-in screen. The message is written completely in Russian, and it fails to mention the file encryption or make any demands. It does, however, provide an email to contact V4cnyy Ransomware’s operators, which is ‘cyber@outlookpro.net.’
Surviving a V4cnyy Ransomware Attack
If you get infected with V4cnyy Ransomware, you should employ a reputable malware remediation device to scan for and remove all elements of this infection.