CLEAN Ransomware Joins the Dharma Ransomware Family
Sometimes malware or ransomware strains are christened with a name that is steeped in irony. Some researchers believe this may have something to do with hackers’ creative sense of humor. One strain of ransomware that bears such a name is CLEAN Ransomware. The name is truly ironic because the intentions of the hackers behind it are totally dirty!
CLEAN Ransomware is a variant from the Dharma Ransomware family. CLEAN Ransomware operates in a manner similar to any classic threat from the Dharma group. It infiltrates the targeted computer, initiates an encryption routine, and locks data.
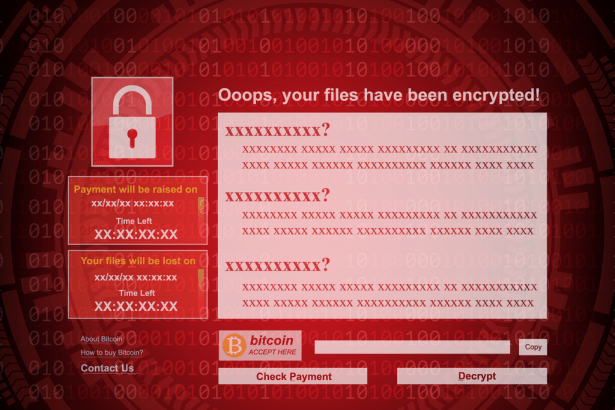
The locked files get their names changed. Affected files will have a unique string of characters representing the unique infection ID, an email address, and ‘.CLEAN’ added to their names. Victims will then find the ransom note in a text file named ‘FILES ENCRYPTED.txt’ in addition to a pop-up window that also displays a slightly different version of the ransom note.
In the ransom notes, cybercriminals try to extort the victims for money by promising to send them the required decryption key and software, but only if the ransom is paid. The ransom amount is not disclosed in the multiple ransom notes. And in a typical Dharma fashion, CLEAN Ransomware’s note lacks most of the vital details that users would need to know.
In fact, the ransom note contains only a few sentences telling victims to message hackers either through ‘clean@onionmail.org’ or ‘clean@privyinternet.com,’ email addresses. Although the alternate pop-up note is longer, it does not provide much more information. It reiterates the same two emails and has an additional section, which gives various warnings, such as not to change the names of the encrypted files, as it can supposedly cause permanent file damage.
How Do I Remove Clean Ransomware from My Computer?
You can scan for and remove elements associated with CLEAN Ransomware and other Dharma-related ransomware strains by using a reputable malware remediation tool.