Nqsq Ransomware Joins the Ranks of the STOP/Djvu Ransomware Family
Nqsq Ransomware is yet another file-encrypting malware associated with the STOP/Djvu Ransomware family. It has been targeting such personal data as documents, videos, databases, and photos.
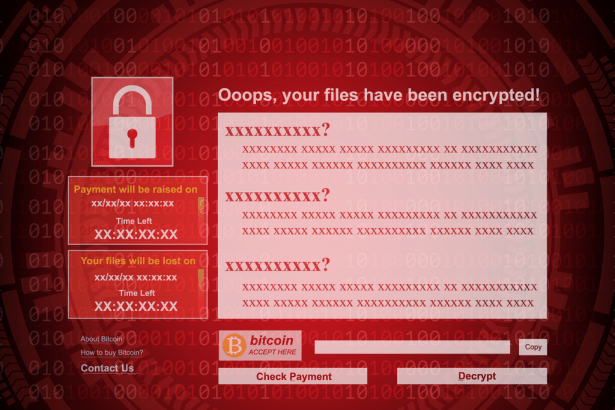
Nqsq Ransomware is identifiable by the telltale .Nqsq extension that it appends to encrypted files. Victims will find that they cannot access these files until the required decryption key or software is activated. The Nqsq Ransomware’s ransom note is left on the affected computer’s desktop and in folders that contain encrypted files. The ransom note is titled “_readme.txt.”
The note says that the victims must contact the hackers behind the infection through the emails:helpmanager@airmail.cc or helpteam@mail.ch. The note also states that to receive a decryption key to unlock the affected files, users must pay either $980 or $490 in Bitcoin, depending on whether they contact the hackers within the first 72 hours after the infection.
The hackers behind Nqsq Ransomware offer to decrypt one file for free as proof that they can offer decryption for all affected files. This is a common tactic across multiple ransomware infections. Affected users would have to email the file to one of the previously mentioned emails to decrypt that one file. However, we do not recommend making contact with hackers at all.
How was I Infected with Nqsq Ransomware?
Usually, victims can get infected with Nqsq Ransomware while visiting torrent websites to obtain pirated or cracked software. Using these dangerous sites isn’t only illegal. Aside from Nqsq Ransomware, you can also unknowingly download Trojans, keyloggers, and other types of malware. What’s more, opening an email attachment from spam or other suspicious emails can also lead to Nqsq Ransomware infection.
How Do I Remove Nqsq Ransomware?
To remove Nqsq Ransomware, you should scan for and remove elements associated with this infection by using reputable malware remediation software. Also, to protect your files from potential future attacks, you should consider backing up your data on an external hard drive or a cloud drive.