Everything You Need to Know About the Trojan.MisplacedLegit.AutoIt Threat and How to Remove It Safely
Malware infections pose a growing danger to computer users worldwide, and among the many threats you could encounter, Trojan.MisplacedLegit.AutoIt has…
Disoaq App: The Malicious Dropper Posing as a PUA
Disoaq App is a Potentially Unwanted Application (PUA) that acts as a dropper for Legion Loader malware. Identified during an…
“Sign-in Attempt Was Blocked” Email Scam
Cybersecurity is increasingly crucial in today's digital world, where phishing and scam campaigns target unsuspecting users. One such campaign involves…
D0glun Ransomware: Understanding, Removal, and Prevention
D0glun is a dangerous ransomware-type virus designed to encrypt files on infected systems and demand a ransom payment from victims.…
InvisibleFerret Malware: Removal and Prevention
InvisibleFerret is a dangerous Python-based backdoor malware linked to North Korean cybercriminals. Primarily used for data theft and injecting additional…
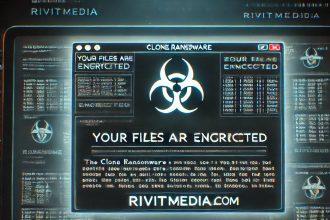
Clone Ransomware: Analysis, Removal, and Prevention
Clone ransomware, a member of the notorious Dharma ransomware family, has been wreaking havoc on computers worldwide. It primarily targets…
Chatsixgirl.com Redirect Virus: Detailed Overview, Removal Guide, and Prevention Tips
Chatsixgirl.com is a harmful website that acts as a browser hijacker, redirecting users to fraudulent links, generating intrusive pop-ups, and…
What Is Helldown Ransomware?
Helldown ransomware is a recently emerged and highly active threat that was first discovered in August 2024. This ransomware group…
Steam.aeonsecho.com: Protection and Removal
Steam.aeonsecho.com is a dangerous website masquerading as an online adult game promotion platform, but it is far from what it…
“Docker Will Damage Your Computer” on Mac: Threat Overview and Removal Guide
Malware targeting Mac users, like the "Docker Will Damage Your Computer" alert, is a growing concern. This intrusive adware disrupts…