The WorldTracker Stealer Threat
Trojan horse malware, commonly referred to as "Trojans," are a form of malicious software designed to infiltrate systems by masquerading…
Prince Ransomware: A Guide to Understanding Ransomware Threats
Ransomware is a form of malicious software designed to block access to a computer system or its data until a…
BlankBot Trojan: A Menacing Threat to Android Devices
Cyber threats are becoming increasingly sophisticated, targeting various platforms and devices. Among these threats is the BlankBot Trojan, a type…
Zola Ransomware: A Comprehensive Guide to Threat and Removal
Ransomware is a form of malicious software designed to block access to a system or personal files until a ransom…
SharpRhino RAT: A Comprehensive Guide to Dealign with Trojans
Trojan horse malware, commonly known as Trojans, are a type of malicious software that disguise themselves as legitimate programs or…
Blue Ransomware: Dealing With File Encryption
Ransomware is a type of malicious software designed to block access to a computer system or its files until a…
Supercharging Your PC: How to Set Up Multiple SSDs for Optimal Performance
So, you’ve been cruising through your digital life with a trusty old hard drive, but lately, it's been feeling more…
Can You Check Browsing History on Your WiFi Router?
We know every click you make leaves a trace, so it’s no wonder that you might want to check browsing…
What is the “About This Image” Tool and How to Use It
In an era where misinformation spreads faster than you can say "Clickbait," Google's "About This Image" tool has emerged as…
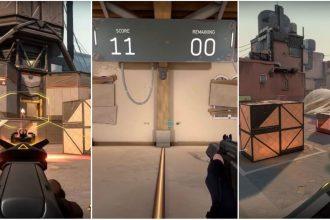
How to Use Aimlabs to Improve Performance in Online Shooters
Are you tired of being the one in your squad who can't hit the broad side of a barn, even…