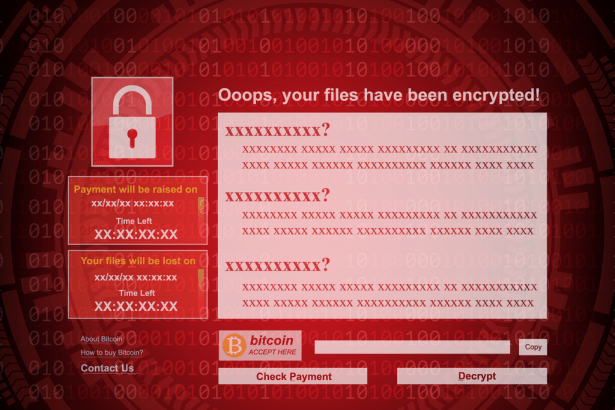
Ransomware continues to be a severe cybersecurity threat, and a new malicious program known as DeathHunters has recently been discovered. This ransomware is based on the Chaos ransomware, encrypts files with a four-character random extension, and demands 1000 euros in Bitcoin for file decryption. Additionally, it uses intimidation tactics, falsely accusing victims of criminal activities, and threatens to leak personal data online.
- DeathHunters Ransomware Overview
- DeathHunters Ransomware
- Ransom Note Text
- How to Remove DeathHunters Ransomware
- Step 1: Isolate the Infected Device
- Step 2: Scan for Malware
- Step 3: Delete Malicious Files and Registry Entries
- Step 4: Restore Files from Backups
- Step 5: Use Shadow Copies (If Available)
- Step 6: Reset Your System (If Necessary)
- Preventing Future Ransomware Attacks
- Enable Strong Security Practices
- Backup Your Files Regularly
- Be Wary of Suspicious Emails & Websites
- Disable Macros in Microsoft Office
- Use Strong Passwords & Multi-Factor Authentication
- Conclusion
- DeathHunters Ransomware
DeathHunters Ransomware Overview
| Attribute | Details |
|---|---|
| Name | DeathHunters Virus |
| Threat Type | Ransomware, Crypto Virus, File Locker |
| Encrypted File Extension | Random four-character extension (e.g., .zypx) |
| Ransom Note File Name | Read_it_or_Death.txt |
| Ransom Demand | 1000 Euros in Bitcoin |
| Bitcoin Wallet Address | 17CqMQFeuB3NTzJ2X28tfRmWaPyPQgvoHV |
| Free Decryptor Available? | No |
| Detection Names | Avast (Win32:RansomX-gen [Ransom]), Combo Cleaner (Gen:Variant.Ransom.Agent.50), ESET-NOD32 (A Variant Of MSIL/Filecoder.Chaos.A), Kaspersky (HEUR:Trojan-Ransom.MSIL.Agent.gen), Microsoft (Ransom:MSIL/FileCoder.AD!MTB) |
| Symptoms of Infection | -Files renamed with random four-character extensions -Inability to access encrypted files -Desktop wallpaper changed with ransom note – Read_it_or_Death.txt file demanding ransom |
| Distribution Methods | Malicious email attachments, torrent downloads, fake software updates, malicious ads |
| Potential Damage | Complete data loss without backups, financial loss, identity theft |

Ransom Note Text
!!! ATTENTION !!!
YOUR SYSTEM IS COMPROMISED
READ WITH CAUTION!!!
HELLO YOU PEDO F**K.
Your System is now Hacked and under our Controll.
You have now 5 Hours to make a Payment of 1000 Euros in Bitcoin to our BTC Adress
and if the Payment is Confirmed by the Virus, it will Give you a Folder on your Desktop Called Viruskiller in which you can find the Programm to Remove the Decryption and Stop the Upload of your Files to our Servers. If Started the Decryption will be Gone and The Virus will be removed, this we Promise. We Dont Like Pedos but we accept your Privacy if you pay.
What will happen if i dont Pay ?
Well... After 5 Hours without Payment Your System will Start to Go Slow and Crazy.. The Virus will
Upload all your Files and Informations about you (Including Historys, Data, Credit, Everthing from You and your System) to our Servers. And we Will Send everthing to the Police and Release everything in the internet and Videos of you Watching Child P.....
OK OK I WILL PAY! What happens after Payment ?
Like we told you you get the Programm to stop and remove the virus.
we delete everthing of you this is Promised.
Where can i Buy Bitcoin ?
Well everywhere in the internet. Coinbase, Binance, Bitpanda etc.
Where to send the Payment of 1000 Euros in Bitcoin to ?
HERE: THIS IS OUR BITCOIN ADRESS:\n17CqMQFeuB3NTzJ2X28tfRmWaPyPQgvoHV
The Payment can take some time to be Received but the Virus will do everething automatically, Dont worry. We Promise to be there for you.
Best Wishes and Good Luck from Team: DEATHHUNTERSHow to Remove DeathHunters Ransomware
Step 1: Isolate the Infected Device
- Disconnect from the internet immediately.
- Unplug external storage devices (USB drives, external hard disks).
- Boot the system into Safe Mode with Networking:
- Restart your computer.
- Press
F8orShift + F8before Windows starts loading. - Select Safe Mode with Networking.
Step 2: Scan for Malware
- Download a trusted anti-malware tool such as SpyHunter.
- Perform a full system scan and remove detected threats.
Step 3: Delete Malicious Files and Registry Entries
- Press
Win + R, typeregedit, and hit Enter. - Navigate to:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunHKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- Look for suspicious entries and delete them.
Step 4: Restore Files from Backups
If you have backups stored on an external drive or cloud service, restore your files.
Step 5: Use Shadow Copies (If Available)
- Right-click on an encrypted file.
- Select Properties > Previous Versions.
- Restore an earlier version if available.
Step 6: Reset Your System (If Necessary)
If the infection persists, consider performing a system restore or reinstalling Windows.
Preventing Future Ransomware Attacks
Enable Strong Security Practices
- Use reputable antivirus software with real-time protection.
- Keep your operating system and software updated.
- Enable firewall and network security settings.
Backup Your Files Regularly
- Store backups in multiple locations (cloud storage, external hard drives).
- Use offline backups to prevent ransomware encryption.
Be Wary of Suspicious Emails & Websites
- Avoid clicking on unknown email attachments and links.
- Download software only from official sources.
Disable Macros in Microsoft Office
- Open Microsoft Word/Excel, go to Options > Trust Center > Trust Center Settings > Macro Settings, and disable macros.
Use Strong Passwords & Multi-Factor Authentication
- Use unique and complex passwords for all accounts.
- Enable multi-factor authentication (MFA) for extra security.
Conclusion
DeathHunters ransomware is a severe threat that encrypts files and demands ransom through intimidation tactics. Paying the ransom is not recommended, as there is no guarantee of file recovery. Instead, victims should focus on removing the ransomware using anti-malware tools, restoring files from backups, and enforcing preventive measures to avoid future infections.